The National Institute of Standards and Technology says it will publish the Ascon group of algorithms in its lightweight cryptography standard later this year.
WHY IT MATTERS
NIST has found “a worthy defender” of data generated by small Internet of Things-connected devices as the result of a four-year international competition, according to the announcement.
In March 2019, NIST received 57 submissions and led a multi-round review process to examine and test the crypto.
Ascon, designed by a team of cryptographers from Graz University of Technology, Infineon Technologies, Lamarr Security Research and Radboud University, was one of 10 finalists.
According to the Computer Security Resource Center, the needed algorithms for symmetric crypto applications require authenticated encryption with associated data.
AEAD allows data collectors, like hospitals, to check the integrity of both the encrypted and unencrypted information being sent from tiny devices and sensors.
“Small devices have limited resources, and they need security that has a compact implementation,” said Kerry McKay, NIST computer scientist leading the effort.
NIST also requested that if a competitor used hash functions to create digital fingerprints of data, the function should share resources with the AEAD to reduce implementation costs.
Ascon is a family of authenticated encryption and hashing algorithms designed to be lightweight and easy to implement, even with added countermeasures against side-channel attacks, says NIST.
THE LARGER TREND
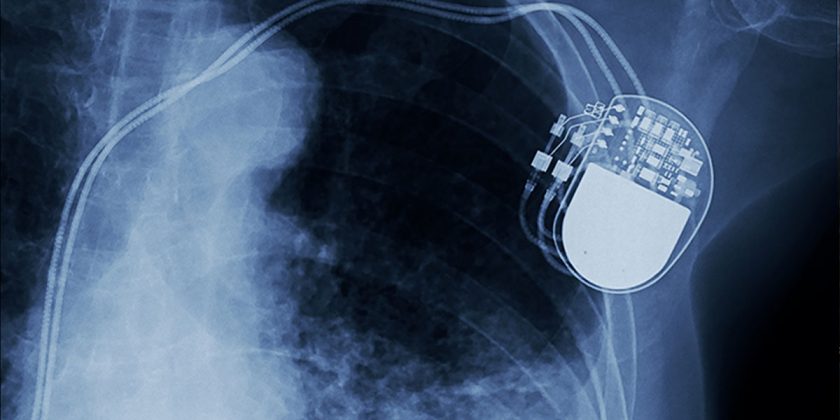
Hospitals report elevated security risks presented by IoT and Internet of Medical Things devices.
The exposure from connected biomedical devices can also open pathways for cybercriminals to take control of hospital systems and cause patient harm.
The proliferation of IoMT devices highlights the need to reinvent data security with cryptographic technology, according to Jamie Wilson, Cryptoloc Technology’s executive chairman and founder.
“With cryptographic technology, no one else has access to the information except for the user themselves,” he previously told Healthcare IT News.
“There’s also a full audit trail where everything is date and time stamped, so you’ll know who has accessed the file and where they have accessed it from.”
ON THE RECORD
“The world is moving toward using small devices for lots of tasks ranging from sensing to identification to machine control,” said McKay in the announcement.
“These algorithms should cover most devices that have these sorts of resource constraints.”
Andrea Fox is senior editor of Healthcare IT News.
Email: [email protected]
Healthcare IT News is a HIMSS Media publication.
Source: Read Full Article